For almost five years, Booking.com customers have been on the receiving end of a continuous series of scams that clearly demonstrate that criminals have obtained travel plans and other personal information customers provided to the travel site.
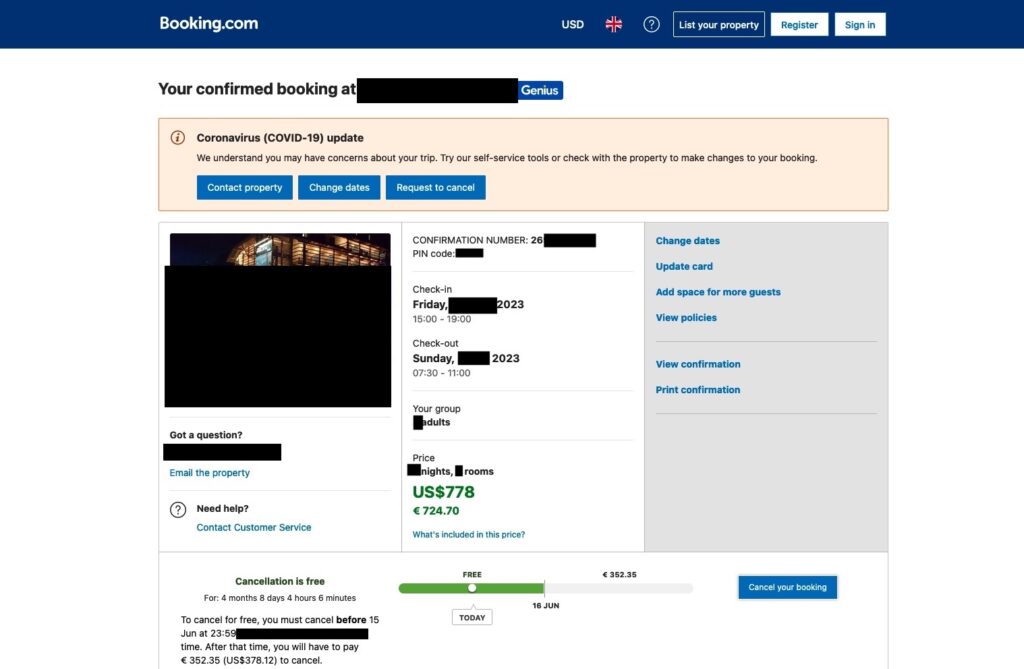
One of the more recent shakedowns happened to an Ars reader who asked not to be identified by his real name. A few months ago, Thomas, as I’ll call him, reserved and paid for a two-night stay scheduled for this July in a hotel in Italy. Here’s the legitimate reservation:
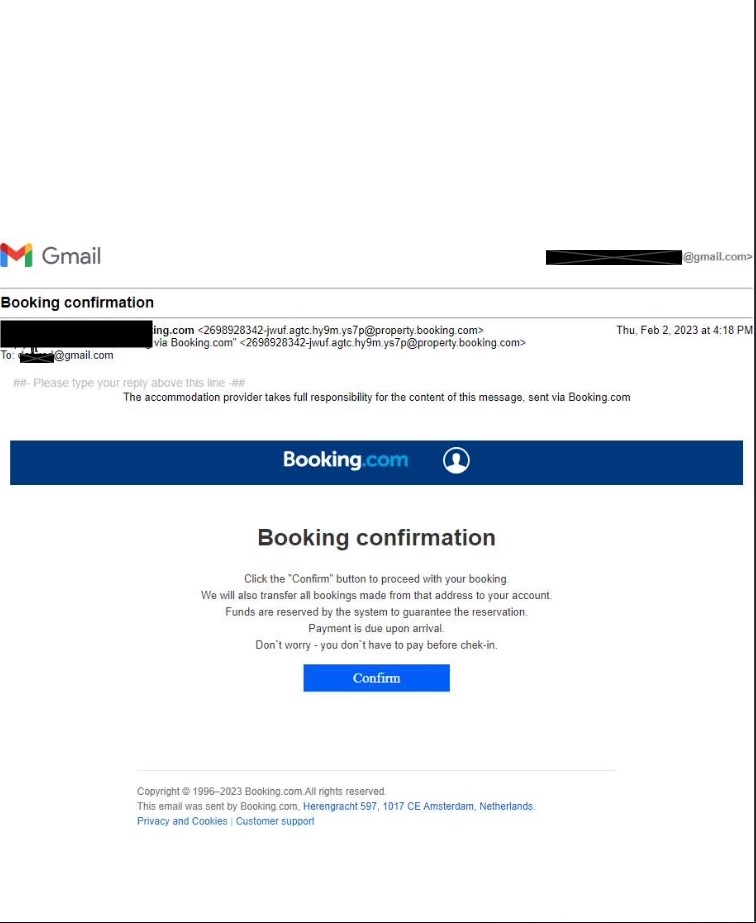
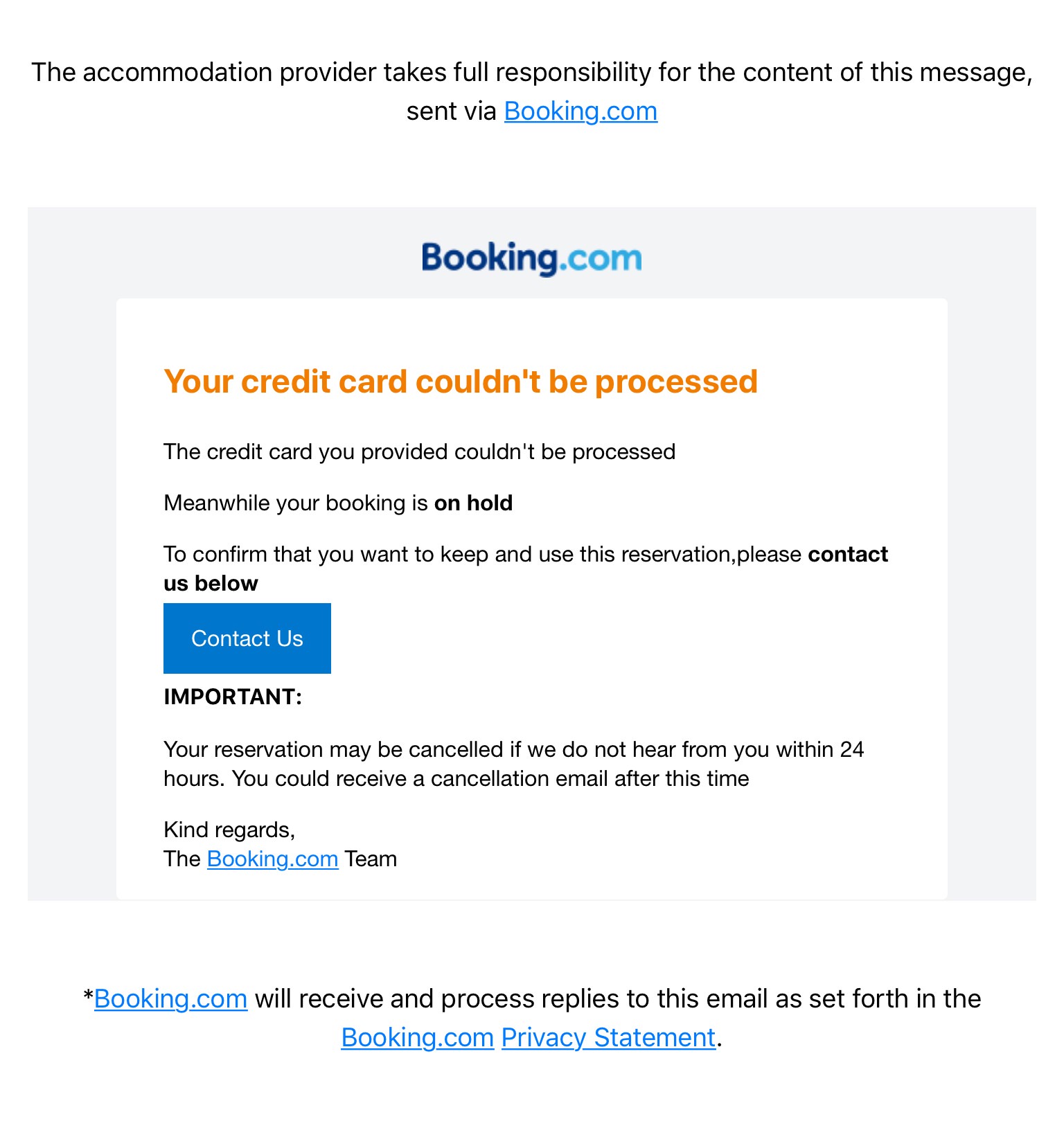
Last week, out of the blue, he received two emails. The headers show that the first message came from the genuine Booking.com domain. It purported to have been sent on behalf of the hotel in Italy and asked that he click a non-existent confirm button for his upcoming stay. It informed him that the hotel would “also transfer all bookings made from that address to your account.” As phishy as that sounds, the email included his full name, the confirmation number of his reservation, the correct name of the hotel, and the dates of his stay.
A second email purported to also have been sent by Booking.com on behalf of the hotel, but headers show that it was sent by an address from yandex.net. The email included the previously mentioned confirmation button that led to a URL that was generated by the Russian shortening service nah.uy.
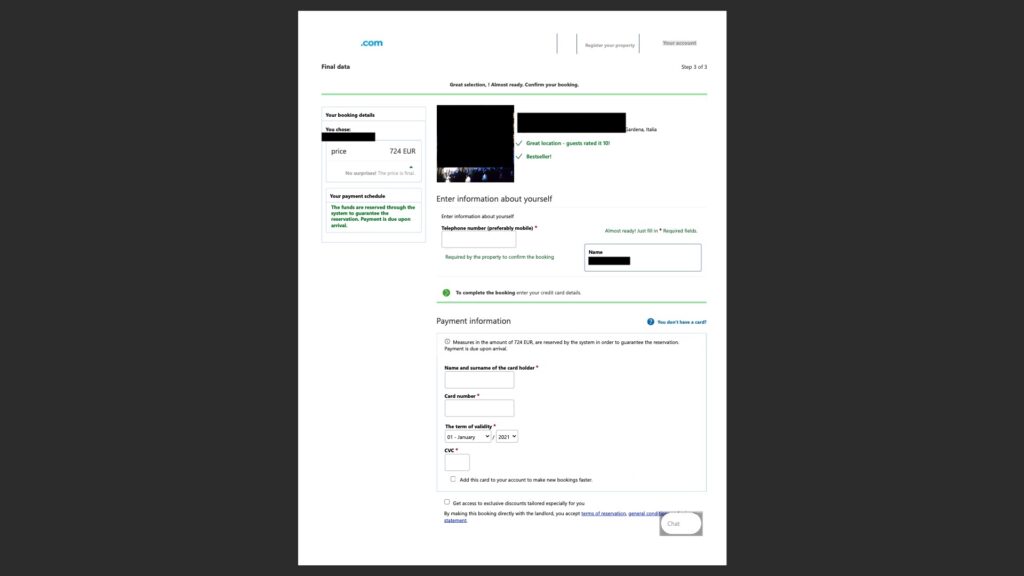
Clicking on the confirm button led Thomas to an almost perfect replica of the real Booking.com webpage. It, too, showed his name, the dates and hotel of his stay, and the exact fare he was charged and went on to direct him to enter his payment card.
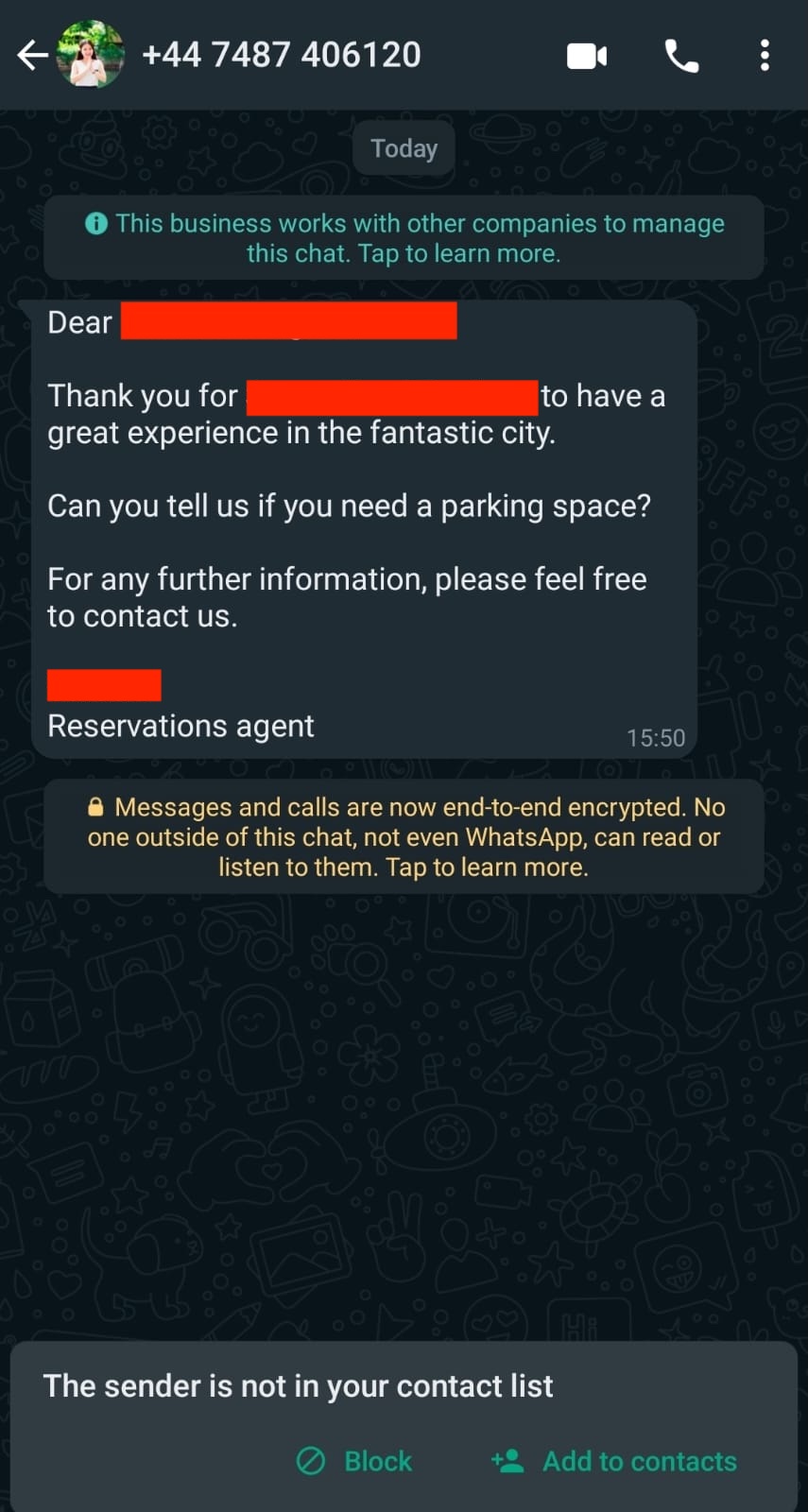
Thomas then received a WhatsApp message sent to the number Booking.com had on file for him. It posed as a message from the hotel he had booked with and asked if he needed parking during his stay.


 Loading comments...
Loading comments...
