Thousands of hacked websites have become unwitting participants in an advanced scheme that uses fake update notifications to install banking malware and remote access trojans on visitors’ computers, a computer researcher said Tuesday.
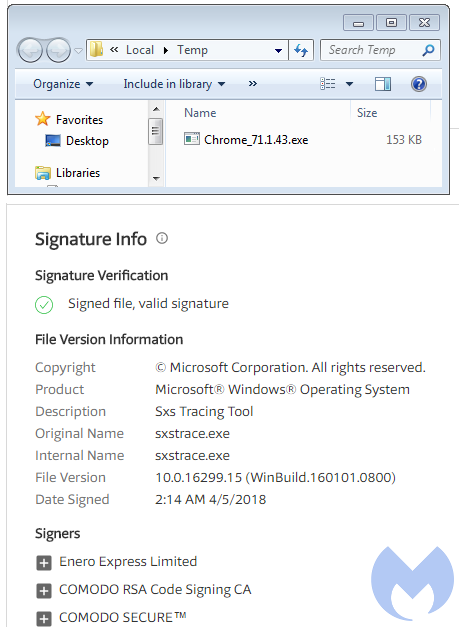
The campaign, which has been running for at least four months, is able to compromise websites running a variety of content management systems, including WordPress, Joomla, and SquareSpace. That’s according to a blog post by Jérôme Segura, lead malware intelligence analyst at Malwarebytes. The hackers, he wrote, cause the sites to display authentic-appearing messages to a narrowly targeted number of visitors that, depending on the browsers they’re using, instruct them to install updates for Firefox, Chrome, or Flash.
“This campaign relies on a delivery mechanism that leverages social engineering and abuses a legitimate file-hosting service,” Segura wrote. “The ‘bait’ file consists of a script rather than a malicious executable, giving the attackers the flexibility to develop interesting obfuscation and fingerprinting techniques.”
Flying under the radar
The attackers also fly under the radar by using highly obfuscated JavaScript. Among the malicious software installed in the campaign was the Chthonic banking malware and a trojanized version of the NetSupport commercial remote access application.


 Loading comments...
Loading comments...
