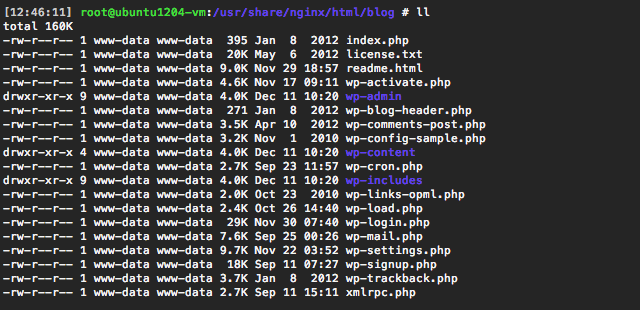
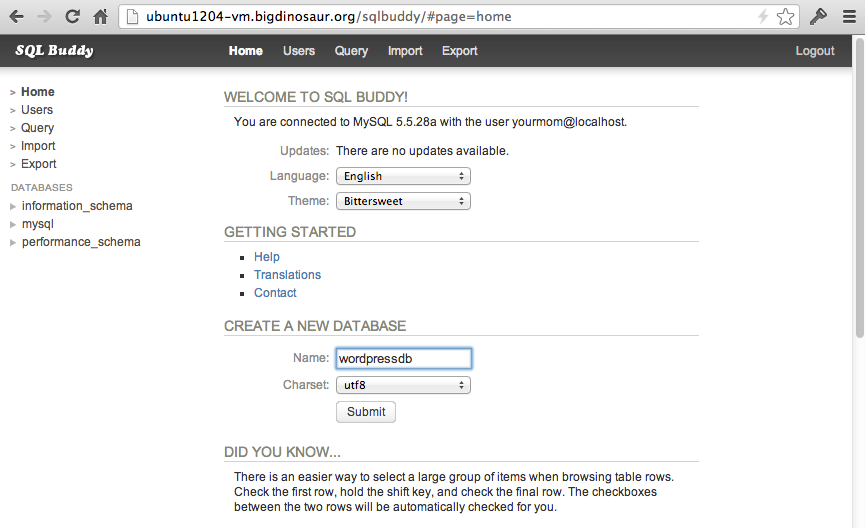
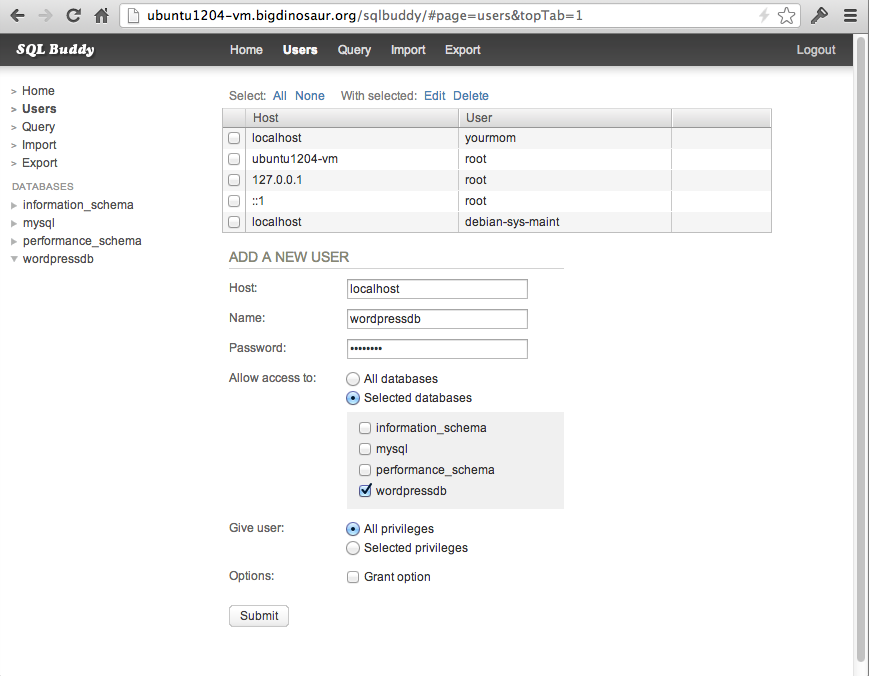
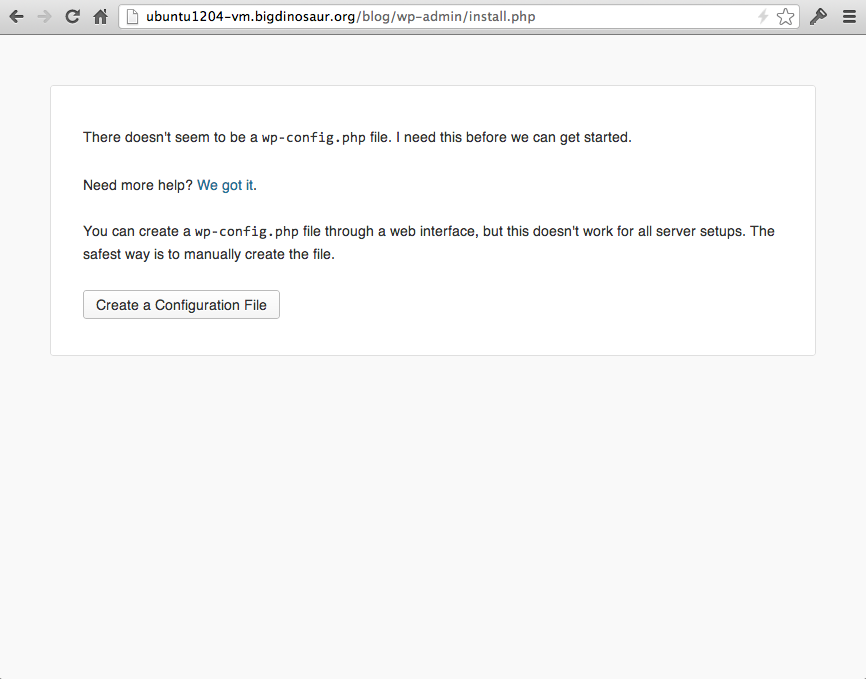
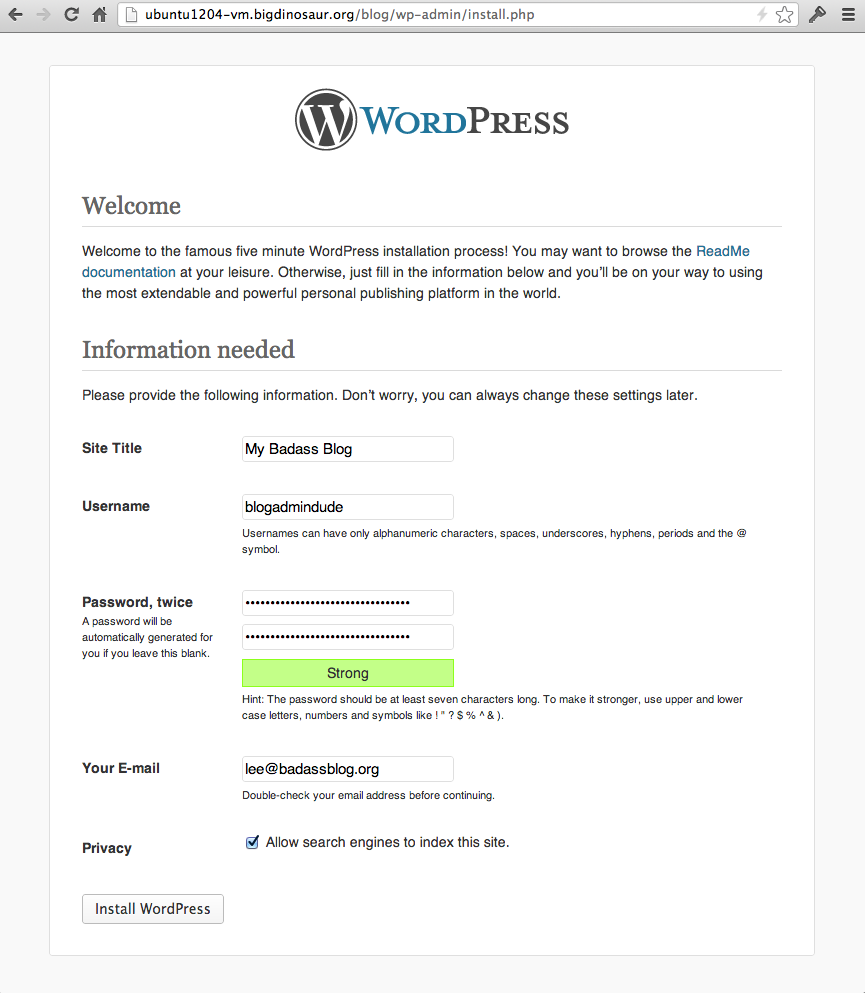
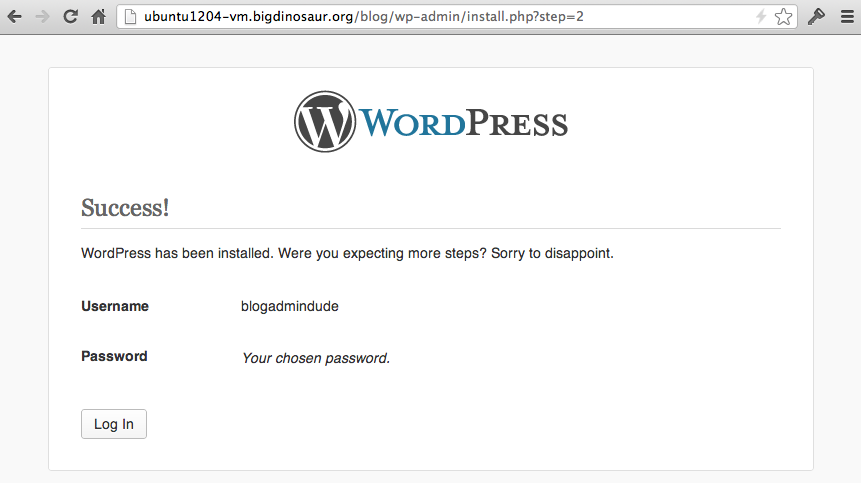
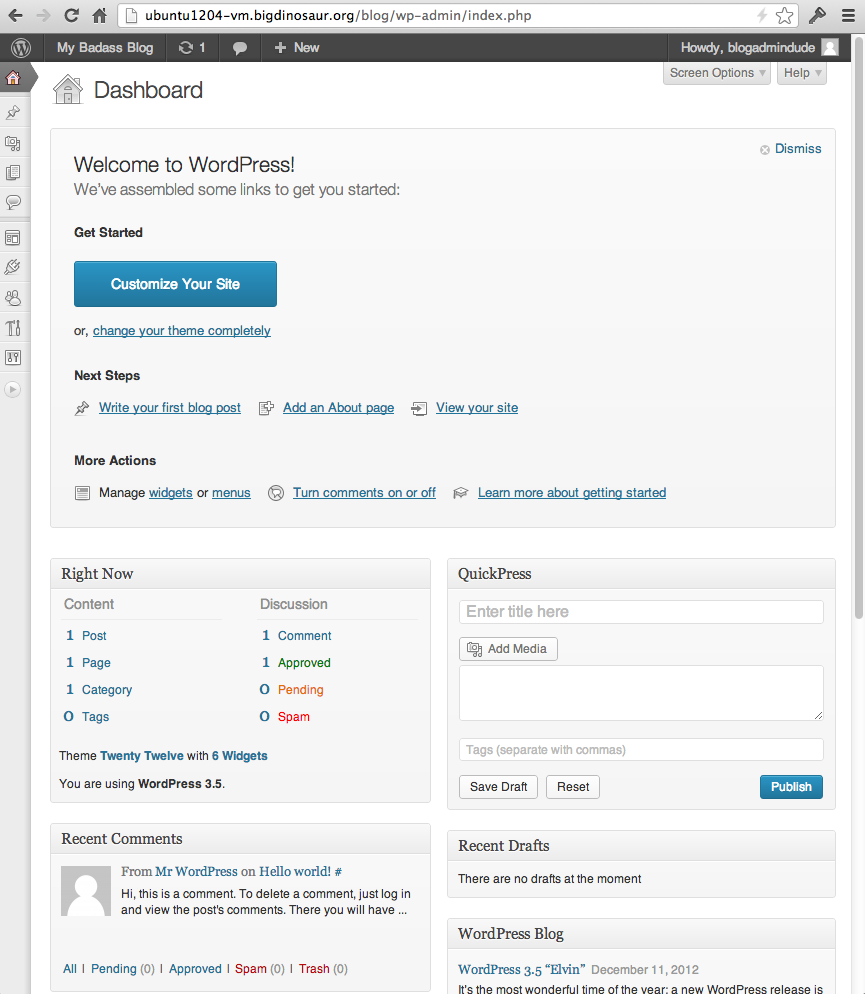
We’ve got a Web server. We’ve got SSL/TLS. We’ve got PHP. We’ve got a database. Now, finally, it’s time to do something with them: we’re going to set up self-hosted WordPress, one of the Internet’s most popular blogging platforms.
Certainly, WordPress isn’t the only choice. There are many blogging platforms out there, ranging from big and full-featured content management systems (like WordPress, Drupal, or Joomla) to static site generators like Jekyll (and its customized variant Octopress, which I use on my own blog). However, WordPress is extremely popular, and it also has a wealth of themes and plugins available with which you can customize its behavior. So, because it’s the platform that first comes to mind when people think of “blogging,” we’re going for it.
Disclosure, and a word on security
This isn’t the first time I’ve talked about setting up WordPress. Some parts of this article will be taken from my previous blog post on the subject, though the instructions here will contain a number of improvements.
We also need to talk about security. WordPress gets kind of a bad rap about being absolutely riddled with security holes. That’s not entirely fair—vulnerabilities in the base platform are rarely the cause of WordPress blog compromises. Rather, WordPress’s huge library of add-ons is both its greatest asset and also its greatest weakness: security issues in WordPress are more often due to a hole in a plugin than a hole in WordPress itself.
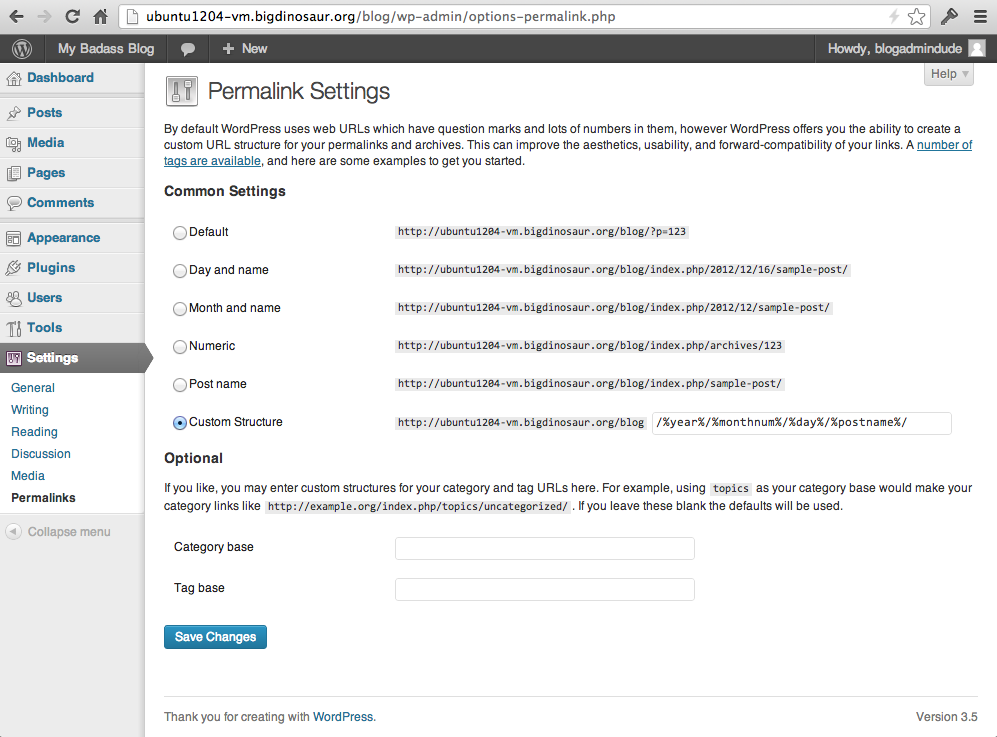
What can we do to help keep things secure? I’ve said it before in this guide and I’ll continue to say it: no system is completely secure, but there are things that can be done to mitigate risk. The first, and most obvious, is to minimize the plugins you use with WordPress. Use what you need and no more. Next, keep your WordPress installation and your installed plugins up to date. Finally, lean on your Nginx configuration to guard against common attack vectors. This last point is one we’ll focus heavily on.




 Loading comments...
Loading comments...
