Scammers have been caught using a clever sleight of hand to impersonate the website for the Brave browser and using it in Google ads to push malware that takes control of browsers and steals sensitive data.
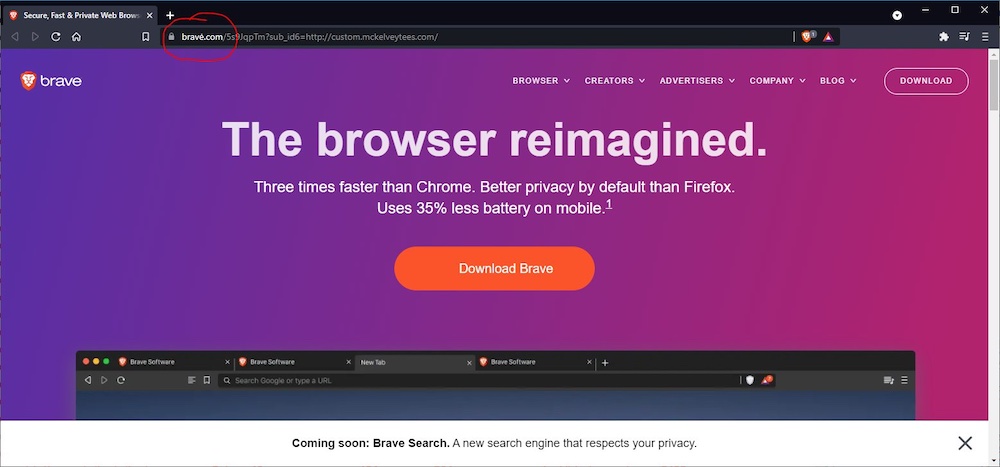
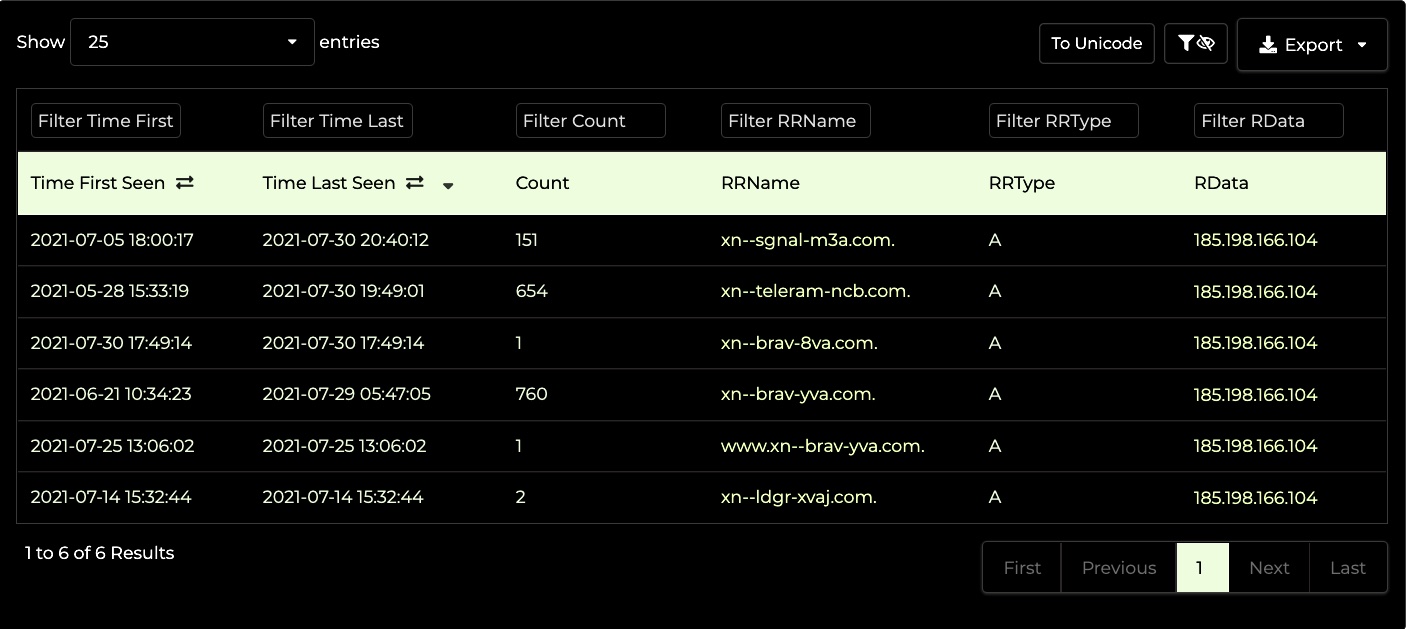
The attack worked by registering the domain xn--brav-yva[.]com, an encoded string that uses what’s known as punycode to represent bravė[.]com, a name that when displayed in browser address bars is confusingly similar to brave.com, where people download the Brave browser. Bravė[.]com (note the accent over the letter E) was almost a perfect replica of brave.com, with one crucial exception: the “Download Brave” button grabbed a file that installed malware known both as ArechClient and SectopRat.
From Google to malware in 10 seconds flat
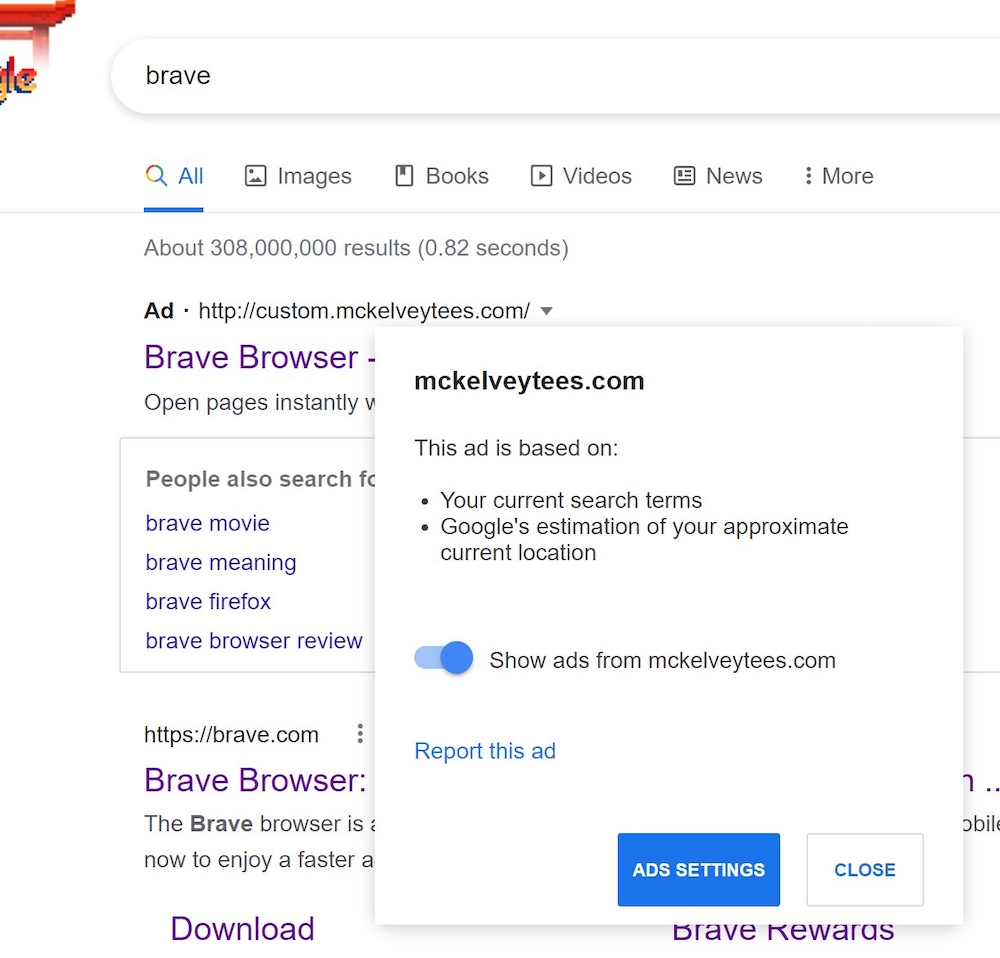
To drive traffic to the fake site, the scammers bought ads on Google that were displayed when people searched for things involving browsers. The ads looked benign enough. As the images below show, the domain shown for one ad was mckelveytees.com, a site that sells apparel for professionals.
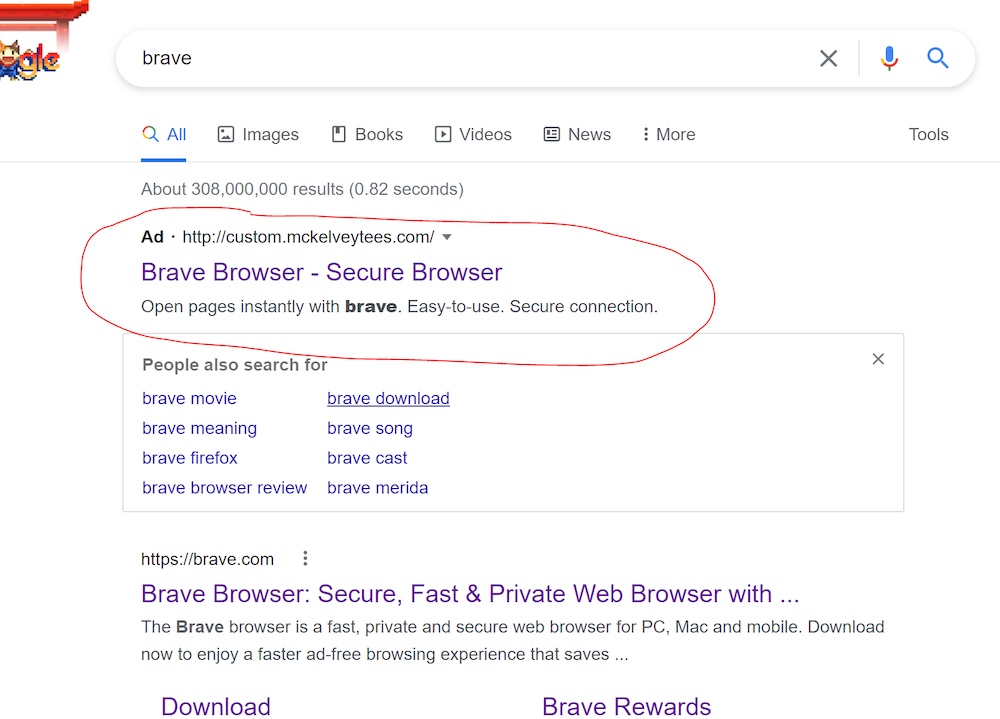
But when people clicked on one of the ads, it directed them through several intermediary domains until they finally landed on bravė[.]com. Jonathan Sampson, a web developer who works on Brave, said that the file available for download there was an ISO image that was 303MB in size. Inside was a single executable.
VirusTotal immediately showed a handful of antimalware engines detecting the ISO and EXE. At the time this post went live, the ISO image had eight detections and the EXE had 16.
The malware detected goes under several names, including ArechClient and SectopRat. A 2019 analysis from security firm G Data found that it was a remote access trojan that was capable of streaming a user’s current desktop or creating a second invisible desktop that attackers could use to browse the Internet.


 Loading comments...
Loading comments...
