The highlight of last year’s Awesome Games Done Quick (AGDQ), the annual weeklong marathon of video game speedrunning, was easily the block run by TASBot (short for tool-assisted speedrun robot). The moment when that emulator-fueled robot hacked into an unmodified Super Mario World cartridge and hard-coded simple versions of Pong and Snake on the fly, using nothing but standard button inputs, was truly surprising and bewildering to behold.
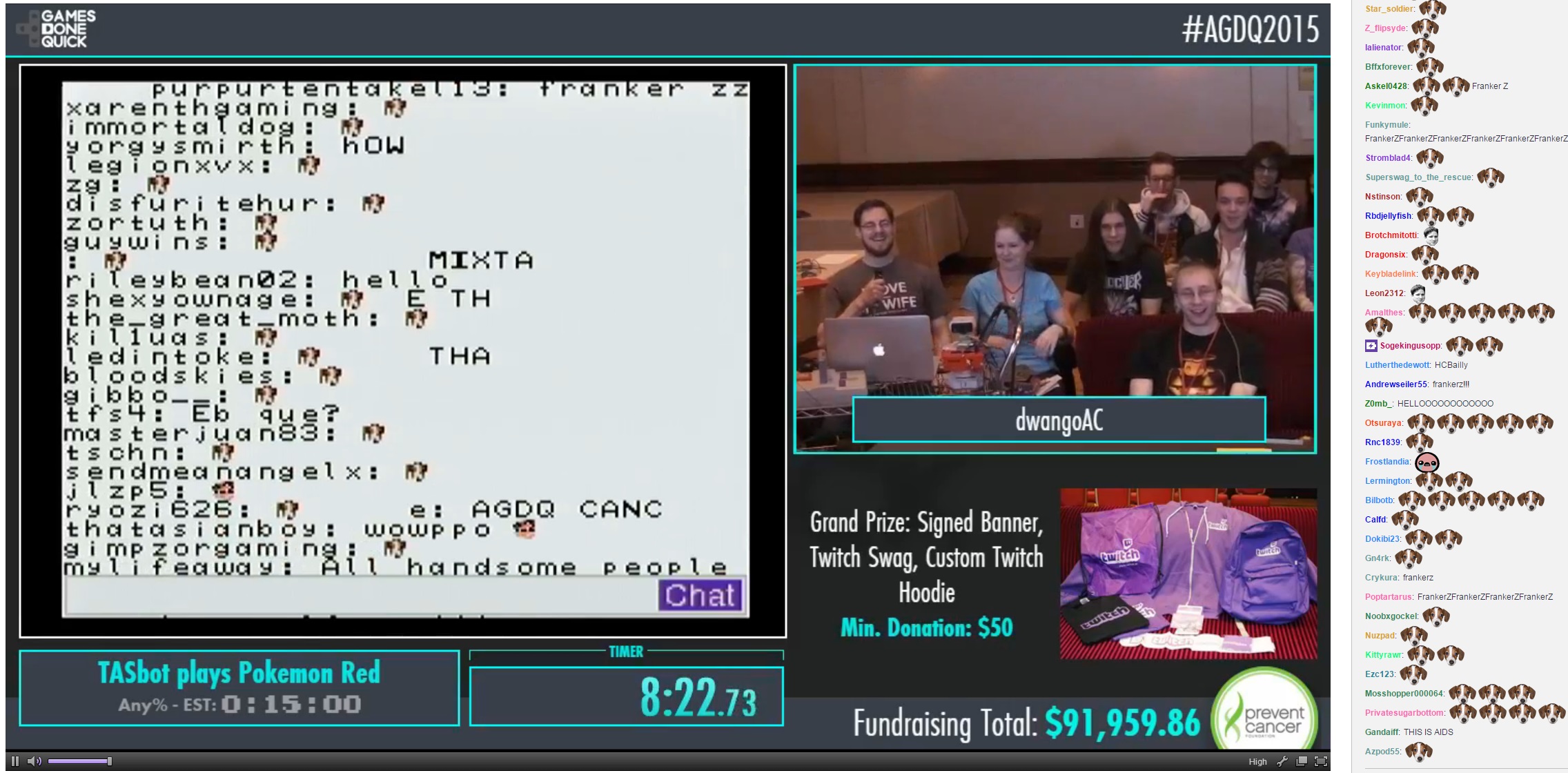
This year, though, the team behind TASBot outdid themselves, showing a new level of mastery over decades-old gaming hardware. As organizer Allan Cecil (a.k.a. DwangoAC) put it during the livestreamed demonstration Sunday night, “We took over Pokémon Red. Then we took over the Super Game Boy. Then we took over the entire Super NES.”
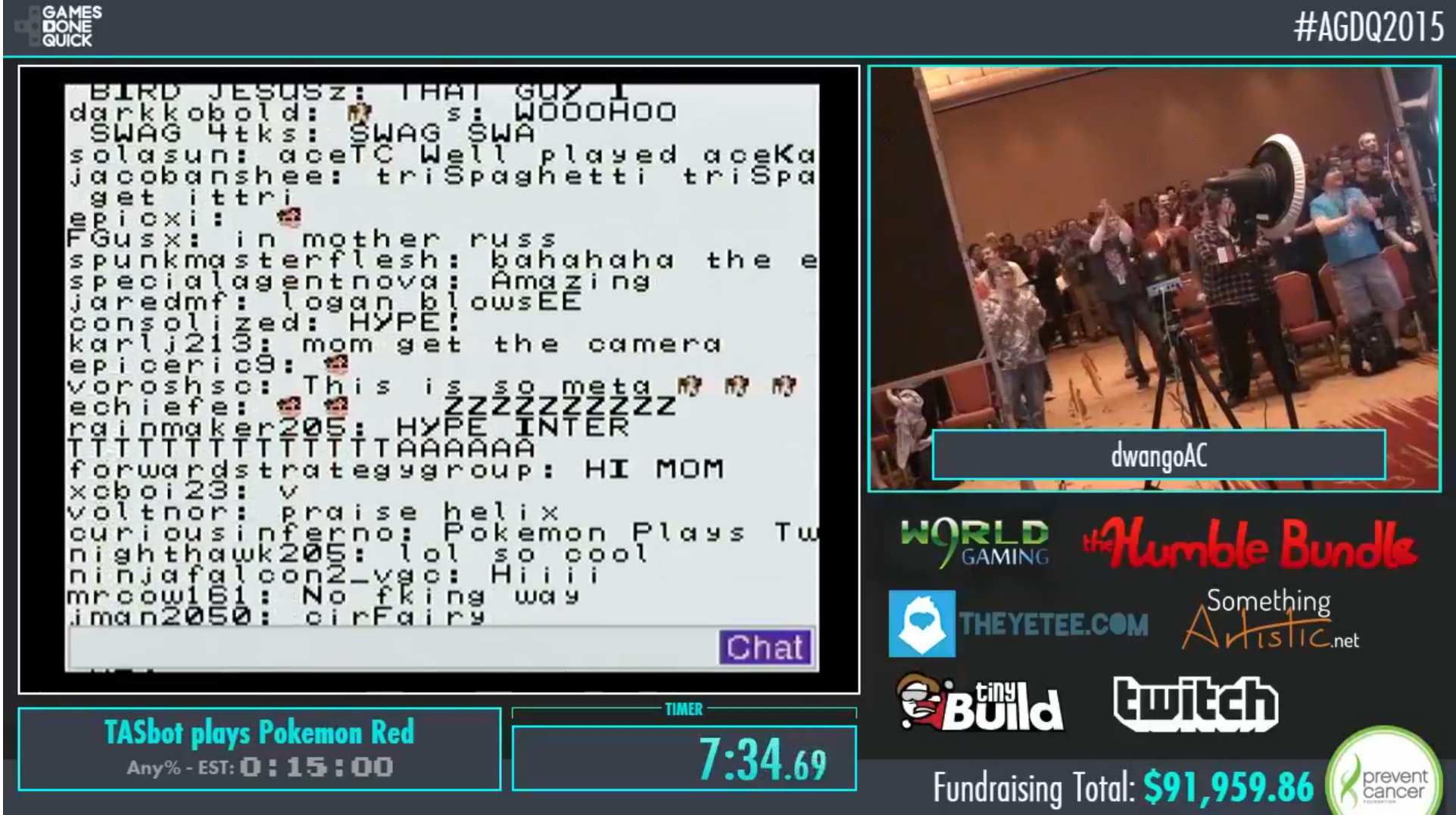
“Then we started streaming [IRC-based] Twitch chat directly through the controller cable.”
You can watch that entire incredible demonstration in action using this Twitch archive link. If you’re hoping to fully follow how the TASBot team used a Game Boy cartridge to get arbitrary code running on a Super NES, though, we should probably back up a bit.
Super Mario Inception
While TASBot is mounted to a classic NES R.O.B. unit, the key to the system is a specially designed “replay board” that can enter inputs into a console at frame-level speed (i.e. 30 or 60 times per second). The inputs being fed into the system are first developed, tested, recorded, and re-recorded on emulators, then played back to the board through a Linux box (in this case a Macbook). While TASBot can enter inputs more quickly and precisely than any human, it’s only sending standard controller signals to the console; there isn’t any hardware-level hacking or memory alteration beyond what is possible through the games and hardware as they originally existed.
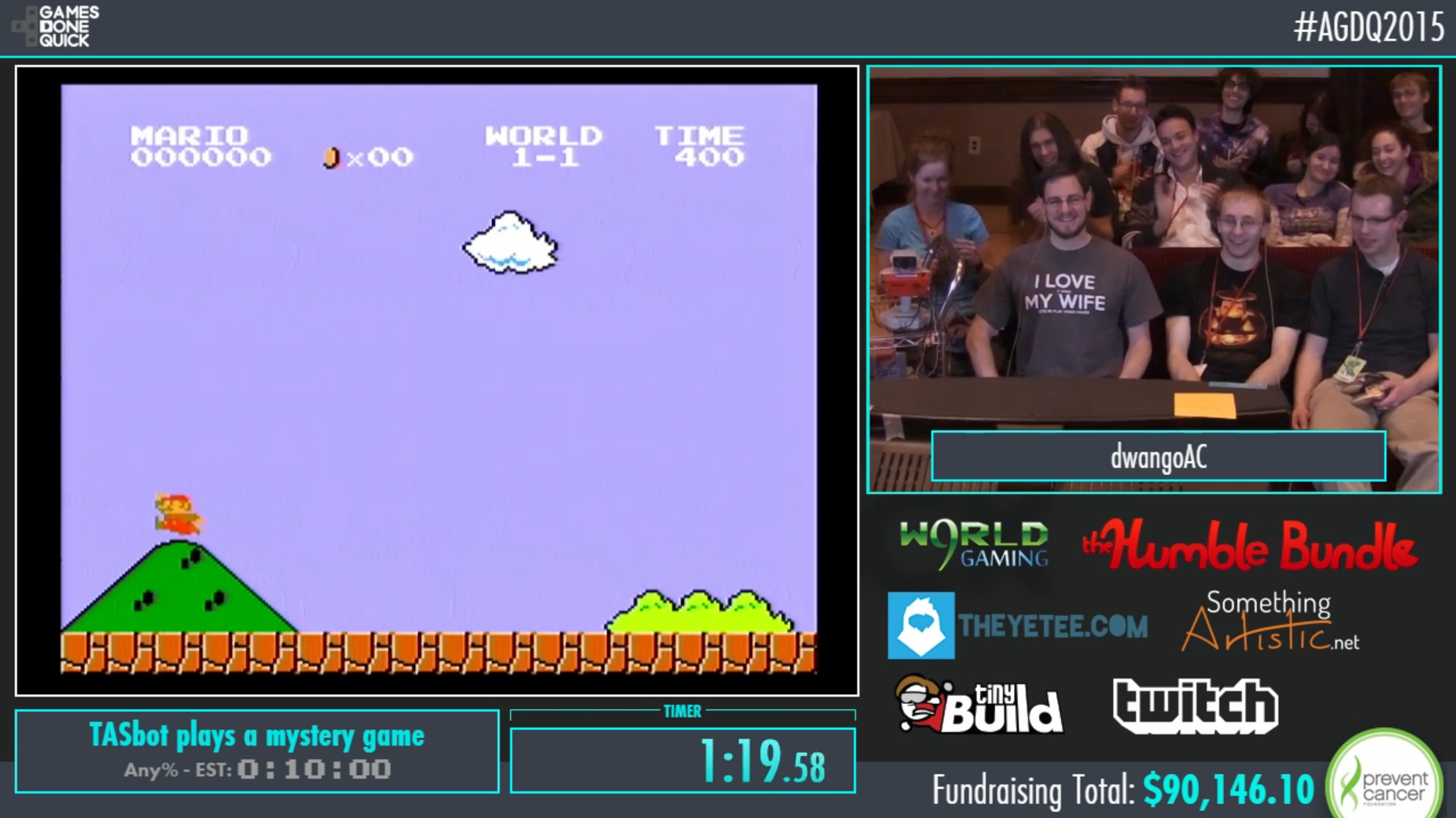
As a preamble during its AGDQ block Sunday night, the TASBot team used its godlike input powers to set up a particularly hazard-filled Choco Mountain course in Mario Kart 64. After that, the team staged a modified repetition of last year’s Super Mario World demonstration, taking “total control” of the game using a series of exploits that got the system to treat the controller input buffer as raw assembly code.



 Loading comments...
Loading comments...
